In an interview conducted by Reporters Without Borders (RSF), technology expert Benjamin Finn warns journalists about the threat posed by metadata and details the available tools for them to protect themselves and their sources.
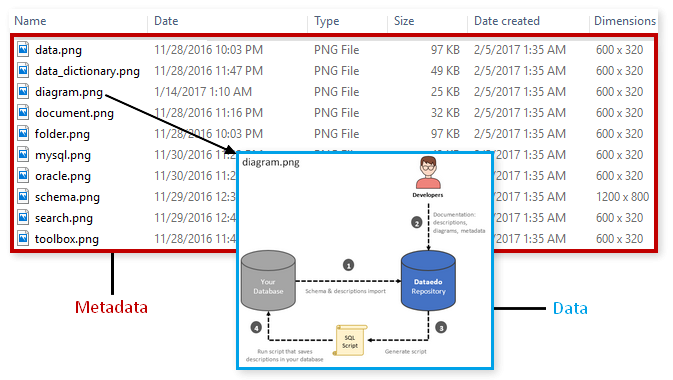
Reporters Without Borders (RSF): What is metadata?
Benjamin Finn (BF:): In its strictest sense, metadata is data that describes data. Different platforms have different metadata needs for their operation, which includes information such as date, time, filename, settings, location, email header, recipient, server names, software and more. It can also include what a user clicks on, how long they stay on a page, what a user purchases, and every trackable habit or interest a user displays. There is metadata on everything a user does on a computer including personal computer files, documents, social media, and in all web searches. These can be combined across multiple platforms using profiles and trackers, also known as cookies, to gain a deep understanding of who someone is and even to predict their online behaviour.
RSF: How can metadata be used for surveillance?
BF: Government authorities may not always be able to access the content of an encrypted conversation, but through metadata they can know the identities of those who are communicating. For example, through an internet service provider (ISP), authorities can access information about who a journalist contacts, their contact’s geolocation and movements, the type of app they’re using and the size of the file being sent, whether it’s encrypted or unencrypted. Though the content of the message itself is inaccessible, the metadata reveals vital information that can be used against both the sender and receiver. Companies such as Google or Facebook pay an extortionate amount for metadata, encouraging apps and internet service providers (ISPs) to collect it from their users. Companies are not interested in what one individual user has to say or do, but being able to take specific statistics from millions of users on their habits, timing, and interests is beneficial for development, sales and marketing.
RSF: Does China’s mass surveillance system exploit metadata?
BF: The government-owned mass surveillance system in China, known as Skynet, monitors its citizens through the internet, surveillance cameras and other digital technologies. Its internal systems were developed using the data -including of course metadata- it collected through WeChat, a multi-purpose instant messaging, social media and mobile payment app widely used by Chinese citizens and diaspora. This piece of technology allows the Chinese government to track users in multiple ways, sometimes even after they leave the country. Artificial intelligence (AI) features have also been added, primarily using metadata from social media activity and browsing history, which allows authorities to “predict” the actions of those they deem problematic.
RSF: Can metadata be encrypted?
BF: No. Generally, metadata cannot be encrypted as it is often needed for an app or website to function. Metadata encryption is a developing technology that many apps do not offer. Virtual private networks (VPNs) can block certain metadata such as an IP address (a unique device identification number) from the app. Beyond that, there are almost no examples of commercially available metadata encryption.
RSF: Are there laws to protect tech users against abusive metadata practices?
BF: No. It is difficult to know which laws a user’s metadata is subject to, as users don’t have control over where their metadata resides. The few laws that do exist to protect metadata are weak or easily bypassed. In 2016, Australia passed a Metadata Retention law which requires ISPs to keep user’s metadata for up to two years, making it available to a range of law enforcement agencies without having to obtain a warrant. This has since proven to be dangerous and has been used to target journalist’s sources without the journalist’s knowledge. A similar metadata law was rejected by the European Union as it was found to violate its Charter of Fundamental Rights.
RSF: How can journalists protect themselves and their sources?
BF: Since ISPs have access to a large amount of information by default, combating privacy issues can be a difficult task. There is no way to completely eliminate the risk of being tracked through metadata, but the following can increase privacy whilst online.
- Use a VPN at all times – a good VPN can mask some metadata such as IP addresses.
- Install apps like Privacy Badger which reduces the tracking systems social media uses, and have a designated device only for social media; but never use it for secure discussions.
- Use a security-focused browser like Brave or Tor; if possible, use the Tor system itself and not just the browser.
- Use security-focused apps for communication like Signal.
- Use encrypted emails like ProtonMail and get sources to do so as well; this email service only has strong protection when used with another ProtonMail account.
- Use burner phones; when not in use, keep powered off with the battery taken out. Be sure to use a different ISP than an everyday phone with a dedicated SIM card.
- Use a physical exchange of large files without directly meeting a source, for example by using a PO box; if meeting a source is necessary, do not bring along any device.
Written by Benjamin Finn. From Houston (USA), Benjamin has been in the IT field for a decade, during which his primary focus was the deployment of internal security tools across large enterprises. Over the last two years, he has been working in Myanmar and researching how to maintain proper security in the context of an oppressive nation-state. In the last few months, he has been working with multiple groups in Taiwan to train them on proper security and safety measures.